SCIM
Updated
by Gina Romero
SCIM
Manage Great Question users directly from your identity provider with automated provisioning, deprovisioning, and group-to-role mapping through SCIM 2.0.
What is SCIM Provisioning?
SCIM (System for Cross-domain Identity Management) lets your identity provider (Okta SAML) automatically create, update, and deactivate Great Question user accounts. Instead of managing users in two places, your IT team controls the full user lifecycle from a single source of truth — your IdP — while Great Question stays in sync.
Why It Matters
Eliminate manual user management. Users are provisioned and deprovisioned automatically from your identity provider. No more separate invites, manual deactivations, or stale accounts.
Strengthen security posture. When someone leaves your organization, their Great Question access is revoked immediately through your IdP — no manual cleanup required.
Give new hires access from day one. Users provisioned through SCIM can access Great Question as soon as they are assigned in your identity provider, with the correct role and team membership already in place.
Keep roles and teams in sync. Map IdP groups to Great Question roles and teams so that access stays consistent as people move across your organization.
How It Works
SCIM provisioning connects your identity provider to Great Question through a secure API endpoint. Once configured, the following syncs happen automatically:
User provisioning — When a user is assigned to the Great Question app in your IdP, their account is created in Great Question with the default role you configure. If a user with that email already exists, the accounts are linked seamlessly.
User deprovisioning — When a user is unassigned or deactivated in your IdP, their Great Question account is deactivated.
Profile sync — Changes to a user's name or email in your IdP are reflected in Great Question in real time.
Group push — IdP groups can be pushed to Great Question and mapped to roles (e.g., "UX Research" → Creator) or teams (e.g., "Oceania" → Oceania team). Three sync modes are available: off, initial sync only, or full continuous sync.
Prerequisites
Before you begin, ensure you have:
- A Great Question Enterprise subscription with SCIM enabled
- Access to Settings > Governance > Provisioning in Great Question (requires Admin role)
- Admin access to your identity provider (Okta SAML)
How to Set Up SCIM Provisioning
Step 1: Generate a SCIM Token in Great Question
- Click your name in the bottom-left corner and select Account.
- Navigate to Governance > Security.
- Click Configure next to SCIM configuration to generate a bearer token and SCIM endpoint URL.
- Copy the SCIM Endpoint URL:
https://api.greatquestion.co/scim/v2 - Copy the SCIM Bearer Token ID — this token is shown only once. Store it securely.

Step 2: Create an App Integration in Okta
- In Okta, go to Applications > Applications.
- Click Create App Integration.
- Select SAML 2.0 (if you also want SSO) or SWA (if you only need provisioning).
- Complete the basic app setup.
Step 3: Configure SCIM in Okta
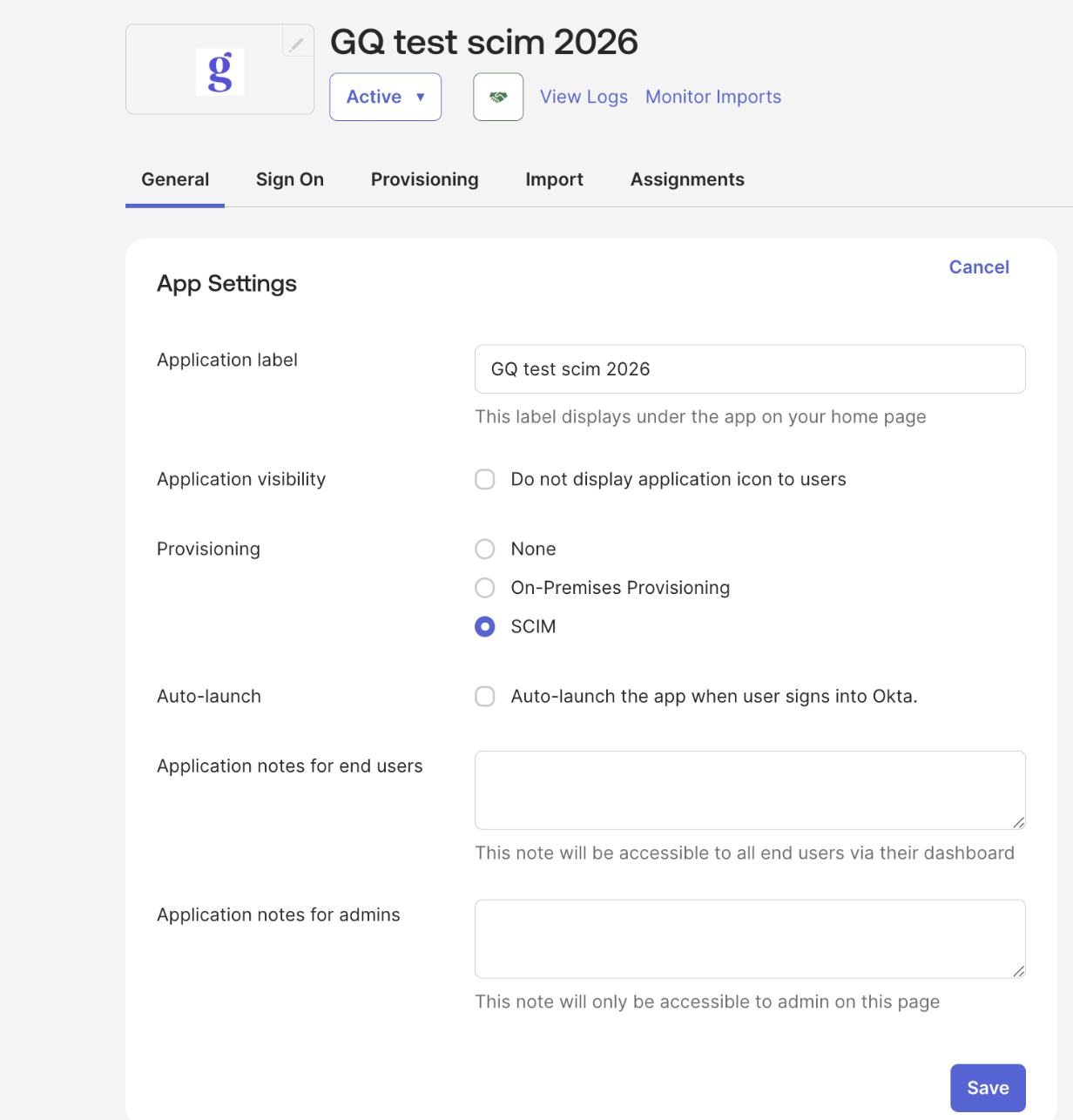
- Open the app you created in Okta and go to the General tab.
- Under App Settings > Provisioning, select SCIM and click Save.
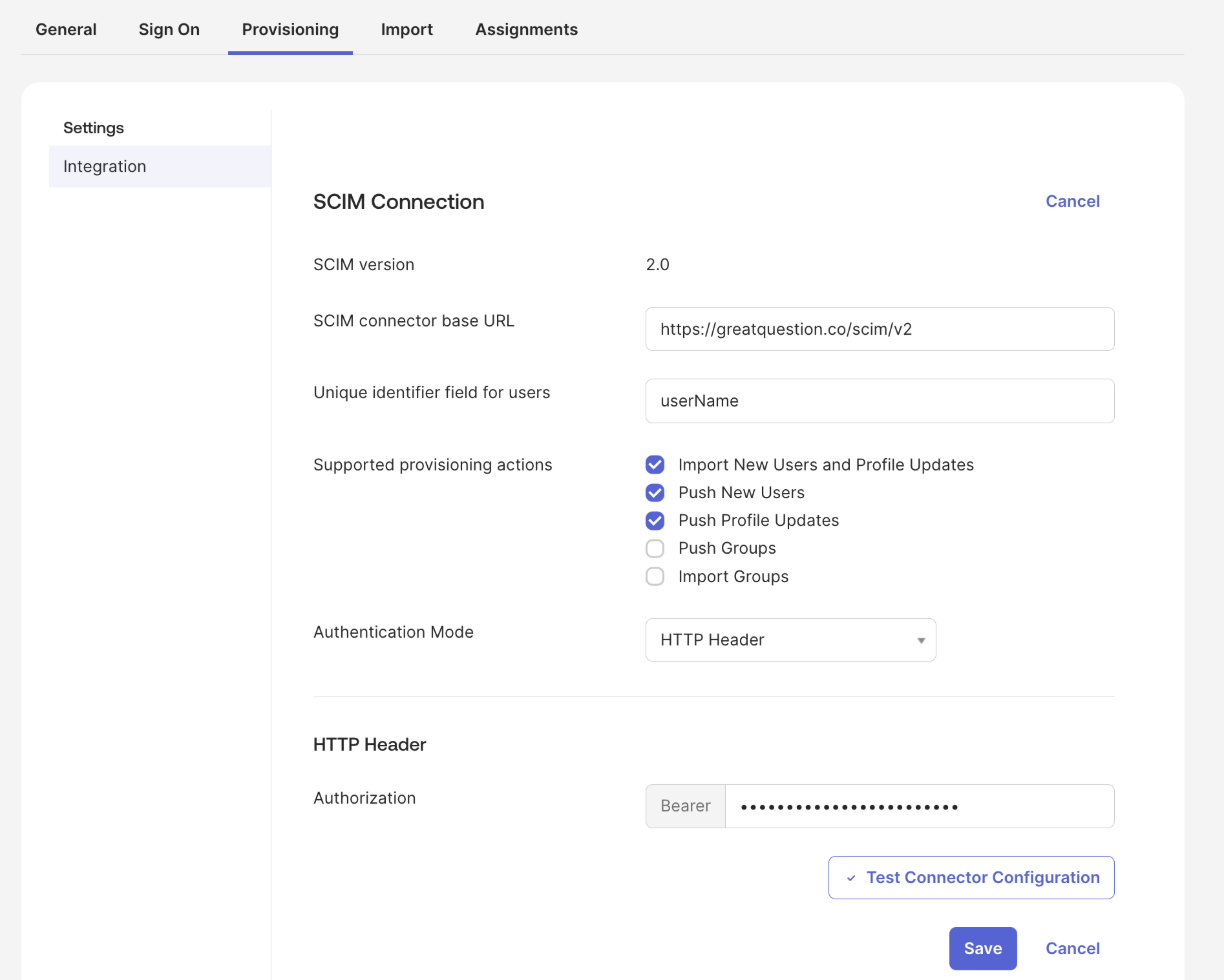
- Go to the Provisioning tab, then click Integration in the sidebar.
- Fill in the following fields:
- SCIM connector base URL: Paste the SCIM Endpoint from Great Question (
https://api.greatquestion.co/scim/v2). - Unique identifier field for users:
userName - Supported provisioning actions: Select Import New Users and Profile Updates, Push New Users, and Push Profile Updates.
- Authentication Mode: HTTP Header
- SCIM connector base URL: Paste the SCIM Endpoint from Great Question (
- Under HTTP Header, paste the Bearer Token you copied from Great Question.
- Click Test Connector Configuration to verify the connection.
- If the test succeeds, click Save.
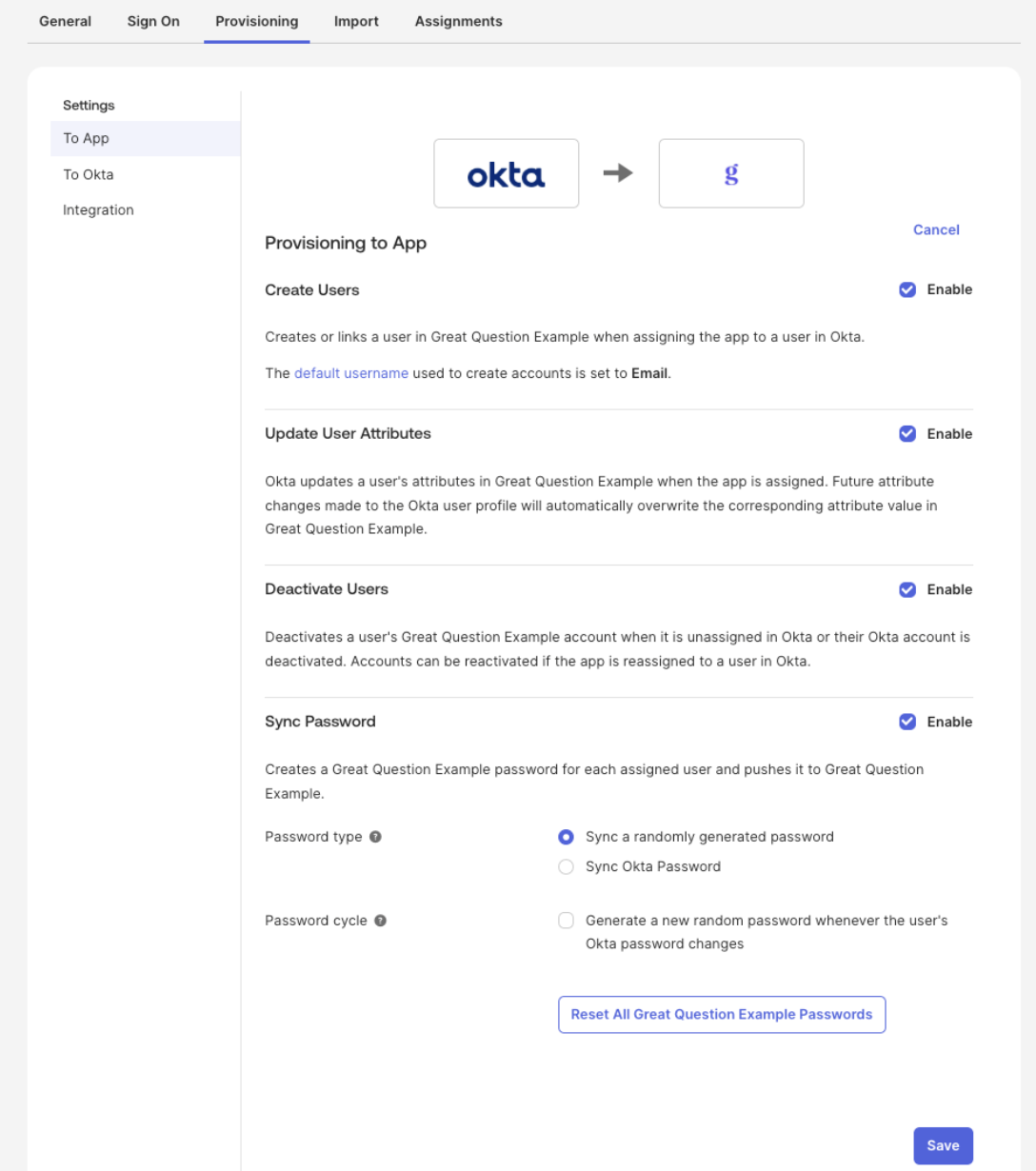
Step 4: Enable Provisioning to App
- Still in the Provisioning tab, click To App in the sidebar.
- Click Edit and enable the following:
- Create Users
- Update User Attributes
- Deactivate Users
- Click Save.
Step 5: Configure Default Role and IdP-Managed Roles
Back in Great Question under Governance > Provisioning:
- Set the Default role for new members created via SCIM. This is the role assigned to any user who does not have a group-to-role mapping. The default is Observer.
- Toggle IdP manages roles on if you want your identity provider to control role assignments through group mappings. When this is enabled, role changes made in Great Question are overwritten on the next sync.
Step 6: Assign Users in Okta
- In Okta, go to the Assignments tab for the Great Question app.
- Click Assign > Assign to People or Assign to Groups.
- Select the users or groups you want to provision and click Assign, then Save and Go Back.
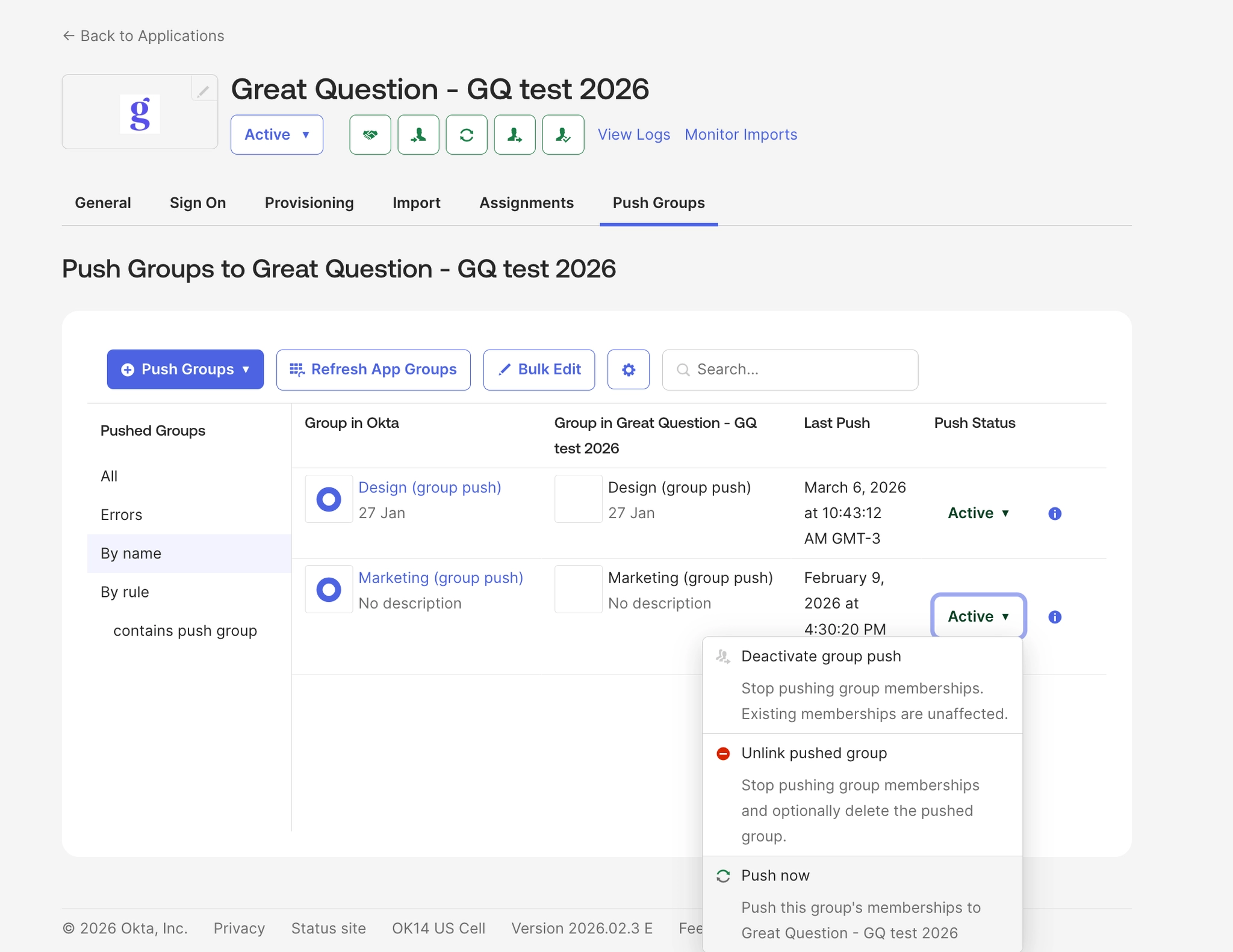
Step 7: Push Groups (Optional)
If you want to sync Okta groups for role or team mapping in Great Question:
- In Okta, go to the Push Groups tab.
- Click Push Groups > Find groups by name.
- Search for and select the groups you want to push, then click Save.
Okta Group Push: Configuration Guide
There are two behaviors to be aware of when configuring Group Push with Great Question.
Groups may arrive without members
This happens when the same Okta group is used for both Application Assignment and Group Push. Okta may push the group before users are fully provisioned, resulting in an empty members list.
- Application Assignment group — used only to provision users into the app
- Group Push group — separate group used only for pushing memberships to Great Question
Membership removals may not sync automatically
When a user is removed from a group in Okta, the change may not immediately reach Great Question. This can happen depending on how users are assigned to the app — if assigned via group rather than directly, Okta may not send the membership removal event. The user may still appear as a group member until the next reconciliation.
SCIM Push Groups Troubleshooting Guide
Problem 1: "Unable to update Group Push mapping target App group"
Error message:
Failed: Unable to update Group Push mapping target App group mgmt-great-question-admin
Root cause: There is a stale push mapping in Okta for the group. The constraint error AppGroups.externalIdAndInstanceKey occurs when Okta tries to create a new mapping for a group that already has a conflicting record in the app instance.
Resolution:
- In Okta, go to Push Groups
- Find the group with the error (e.g.
mgmt-great-question-admin) - Delete the existing push mapping
- Recreate the mapping — when the "Match result & push action" screen appears, select "Create Group" (not "Link Group")
- Click "Push Now"
- Verify the group appears with the correct members at
https://greatquestion.co/governance/scim_groups
Okta reference: https://support.okta.com/help/s/article/Unable-to-update-Group-Push-with-error-Unable-to-update-Group-Push-mapping-target-App-group
Problem 2: Active Okta users failing SCIM provisioning — "User account is inactive"
Error message:
Automatic provisioning of user [X] to app Great Question failed: User account is inactive
Symptom: Users appear active in Okta, but SCIM only sends GET requests (lookups) and group updates — no PUT/POST to /Users. Without a POST/PUT, no SCIM link is created for the user on Great Question's side.
Root cause: The "Deactivate Users" option under Okta's SCIM provisioning settings was not enabled. Without it, Okta cannot properly sync the user's lifecycle state with the app, which blocks provisioning.
Resolution:
- In Okta, go to Applications → Great Question → Provisioning → To App → Edit
- Enable "Deactivate Users" (in addition to "Push New Users" and "Push Profile Updates")
- Save
- Reassign the affected users to the application (individually or via group)
- Confirm provisioning succeeded in the Okta logs
Additional Notes
Groups arriving without members is expected behavior. Groups and their members are synced in separate steps. See: https://greatquestion.co/support/integrations/scim#groups_may_arrive_without_members
Verifying group sync: Use https://greatquestion.co/governance/scim_groups to confirm which groups are synced, how many members they have, and which role is mapped to each
How to Verify SCIM Is Working
Once your IdP is configured, you can confirm everything is connected from the Provisioning settings page in Great Question.
Check the configuration status. The SCIM configuration card shows one of two statuses: Pending means the token has been created but the IdP has not connected yet; Active means the IdP has successfully made its first request.
Review sync details. The configuration card also displays the Synced members count and the Last sync timestamp, so you can confirm that provisioning events are flowing through.
Verify in the Members list. Users provisioned through SCIM appear in the Members list with an IdP-sourced badge, making it easy to distinguish between SCIM-managed and manually-created accounts.
Admin Controls
Setting | Description |
Default role | The role assigned to new users created via SCIM who do not have a group-to-role mapping. Options: Admin, Creator, Observer. |
IdP manages roles | When enabled, user roles are controlled by your identity provider through group mappings. Manual role changes in Great Question are overwritten on the next sync. |
SCIM Endpoint | The URL your identity provider uses to connect: |
SCIM Bearer Token ID | The authentication token for your IdP. Hidden after creation. Regenerating a token invalidates the previous one. |
Regenerate token | Creates a new bearer token and invalidates the old one. You will need to update the token in your IdP after regenerating. |
Edge Cases and Safeguards
Seat limits. If your account reaches its seat limit during provisioning, the new user is assigned the Observer role regardless of their group mapping, and your account Admin is notified. This prevents provisioning failures while keeping access available.
Account owner and last admin protection. SCIM cannot deprovision the account owner or the last remaining Admin on the account. These requests fail safely to prevent lockout.
Existing user linking. If a user provisioned through SCIM already has a Great Question account with the same email, the existing account is linked to the IdP automatically — no duplicate is created.
What happens to open studies when users are deactivated?
With draft studies and panel studies, ownership is transferred to the account owner. With active non-panel studies, study is automatically paused and the deactivated user stays as owner.
Troubleshooting SCIM
Issue | What's Happening | How to fix |
SCIM token status shows "Pending" after configuring the IdP | The IdP has not yet made its first request to the SCIM endpoint | In Okta, click Test Connector Configuration in the Provisioning > Integration settings. Confirm that the SCIM base URL and bearer token match what is shown in Great Question under Governance > Provisioning. Make sure there are no extra spaces in the token and that it has not been regenerated since you pasted it. |
A provisioned user does not appear in Great Question | The user is not assigned to the app in the IdP, provisioning actions are not enabled, or the account has hit its seat limit | In Okta, verify that Create Users is enabled under Provisioning > To App and check provisioning logs (Reports > System Log or the app's Tasks tab). If your account reached its seat limit, the user may have been created as an Observer — check the Members list. |
Deprovisioning a user did not revoke their access | The user is the account owner or last Admin, or the deactivation action is not enabled in the IdP | SCIM cannot deprovision the account owner or last Admin — these requests fail safely. For other users, confirm that "Deactivate Users" is enabled in your IdP's SCIM configuration and check deprovisioning logs for errors. |
I regenerated the SCIM token and provisioning stopped working | The previous token was invalidated immediately when the new one was generated | Update the bearer token in your identity provider's SCIM configuration with the new token. All provisioning requests will fail authentication until the IdP token is updated. |
Pushed group arrives in Great Question with no members | The same Okta group is used for both Application Assignment and Group Push, and Okta pushed the group before users were fully provisioned | Use two separate groups — one for Application Assignment and one for Group Push. Ensure users are provisioned before the group push runs. See the Okta Group Push: Configuration Guide section above for details. |
Group membership removal in Okta is not reflected in Great Question | Okta may not send the membership removal event depending on how users are assigned to the app | Trigger a manual sync from Applications → Push Groups → [select group] → Push Now in Okta. |
Still need help? Contact us at [email protected] — we're happy to help!